Top Crypto Ransomware Payments Report
Crypto Ransomware
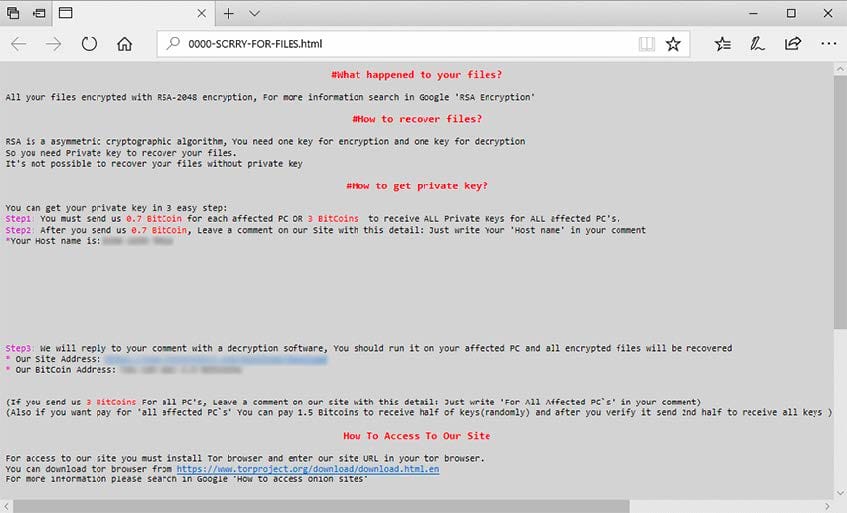
Ransomware attacks use ransomware, which is a form of malware designed to encrypt files on a device or entire network and make them inaccessible. Ransomware groups carry out these attacks and then demand a ransom in return for returning control of those systems.
With the growth of cryptocurrencies like Bitcoin, ransomware attacks saw a noticeable increase in popularity, as ransomware groups have come to believe that cryptocurrency is anonymous, untraceable, and can facilitate much larger ransom payments than traditional financial systems.
Top Crypto Ransomware Payments
The top crypto ransomware payments total $69,316,140 across 10 specific situations.
| Project | Ransom Payment |
|---|---|
| CNA Financial | $40,000,000 |
| JBS | $11,000,000 |
| CWT | $4,500,000 |
| Brenntag | $4,400,000 |
| Colonial Pipeline* | $4,400,000 |
| Travelex | $2,300,000 |
| UCSF | $1,140,895 |
| BRB Bank | $957,245 |
| Jackson County, Georgia | $400,000 |
| University of Maastricht* | $218,000 |
*Colonial Pipeline recovered $2,300,000 from the ransom payment, and the University of Maastricht recovered the full ransom payment amount. When recovered, the total Bitcoin value from Maastricht's payment was worth $510,000.
Overview
| Project | Ransom Payment | Funds Recovery | Ransomware Strain | Cryptocurrency | Origin |
|---|---|---|---|---|---|
| CNA Financial | $40,000,000 | N/A | Phoenix | Bitcoin | Russia |
| JBS | $11,000,000 | N/A | REvil/Sodinokibi | Bitcoin | Russia |
| CWT | $4,500,000 | N/A | Ragnar Locker | Bitcoin | N/A |
| Brenntag | $4,400,000 | N/A | DarkSide | Bitcoin | Eastern Europe |
| Colonial Pipeline | $4,400,000 | $2,300,000 | DarkSide | Bitcoin | Eastern Europe |
| Travelex | $2,300,000 | N/A | REvil/Sodinokibi | Bitcoin | Russia |
| UCSF | $1,140,895 | N/A | Netwalker Ransomware | Bitcoin | N/A |
| BRB Bank | $957,245 | N/A | LockBit | Bitcoin | Eastern Europe |
| Jackson County, Georgia | $400,000 | N/A | SamSam | Bitcoin | Iran |
| University of Maastricht | $218,000 | $218,000* | Clop Ransomware | Bitcoin | Russia |
*When recovered, the total Bitcoin value was worth $510,000.
Top 5 Cases
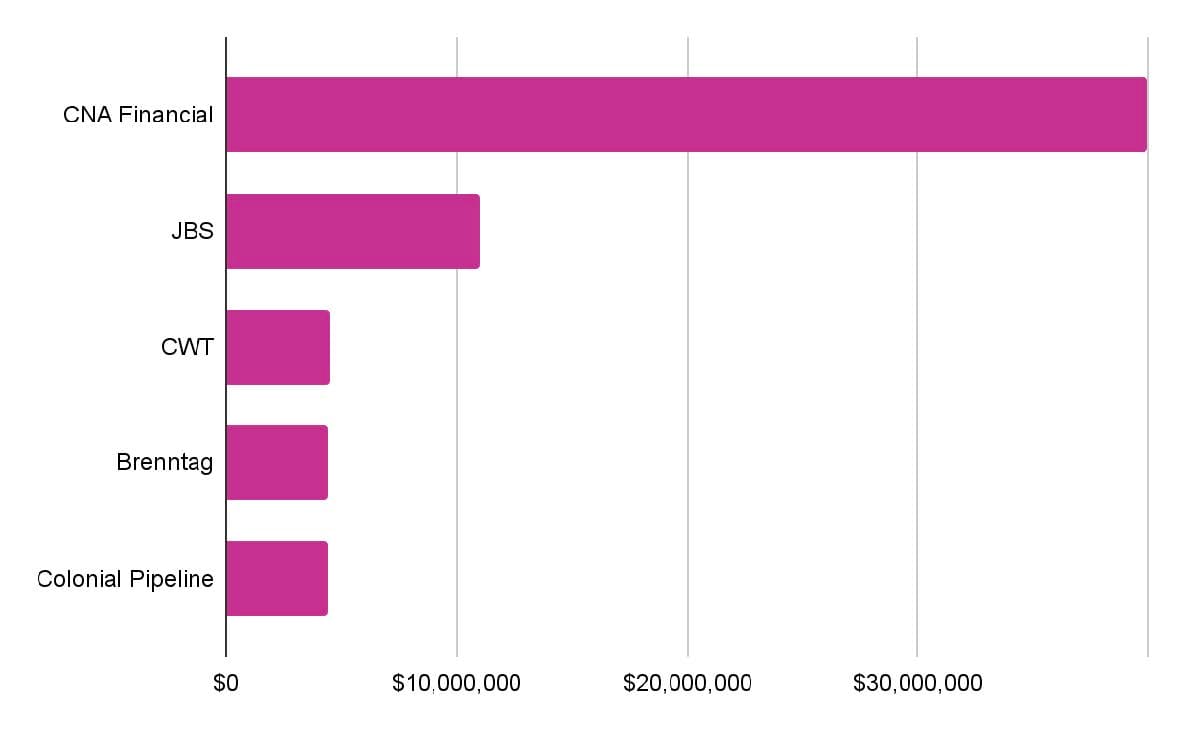
CNA Financial $40,000,000
JBS $11,000,000
CWT $4,500,000
Brenntag $4,500,000
Colonial Pipeline $4,400,000*
*Colonial Pipeline recovered $2,300,000 from the ransom payment.
Ransom Recovery
In total, $2,518,000 has been recovered from ransom payments in 2 specific situations. This number makes up 3.6% of the top crypto ransomware payments.
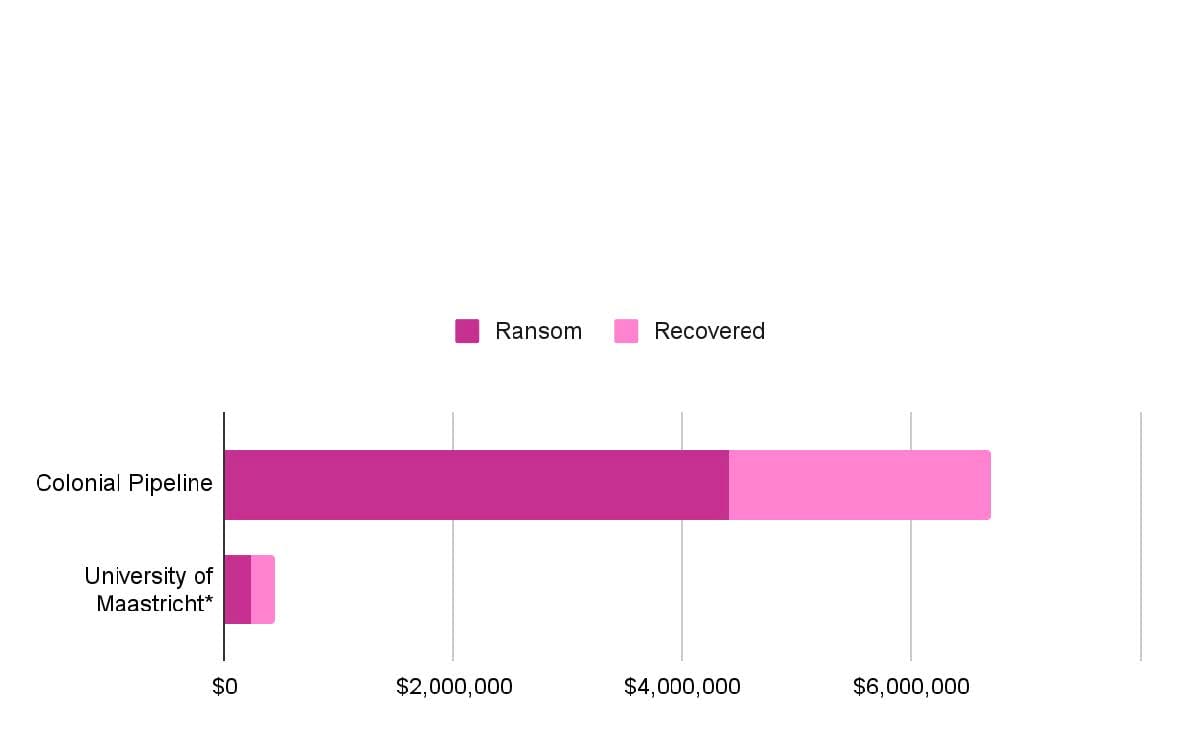
Colonial Pipeline
Ransom $4,400,000
Recovered $2,300,000
University of Maastricht
Ransom $218,000
Recovered $218,000*
*When recovered, the total Bitcoin value was worth $510,000.
Detected Ransomware Strains
Researchers have detected 8 specific strains of ransomware connected to the top crypto ransomware payments. REvil/Sodinokibi and DarkSide are key actors based on the total number of attacks, but the Phoenix group had the highest profiting attack.
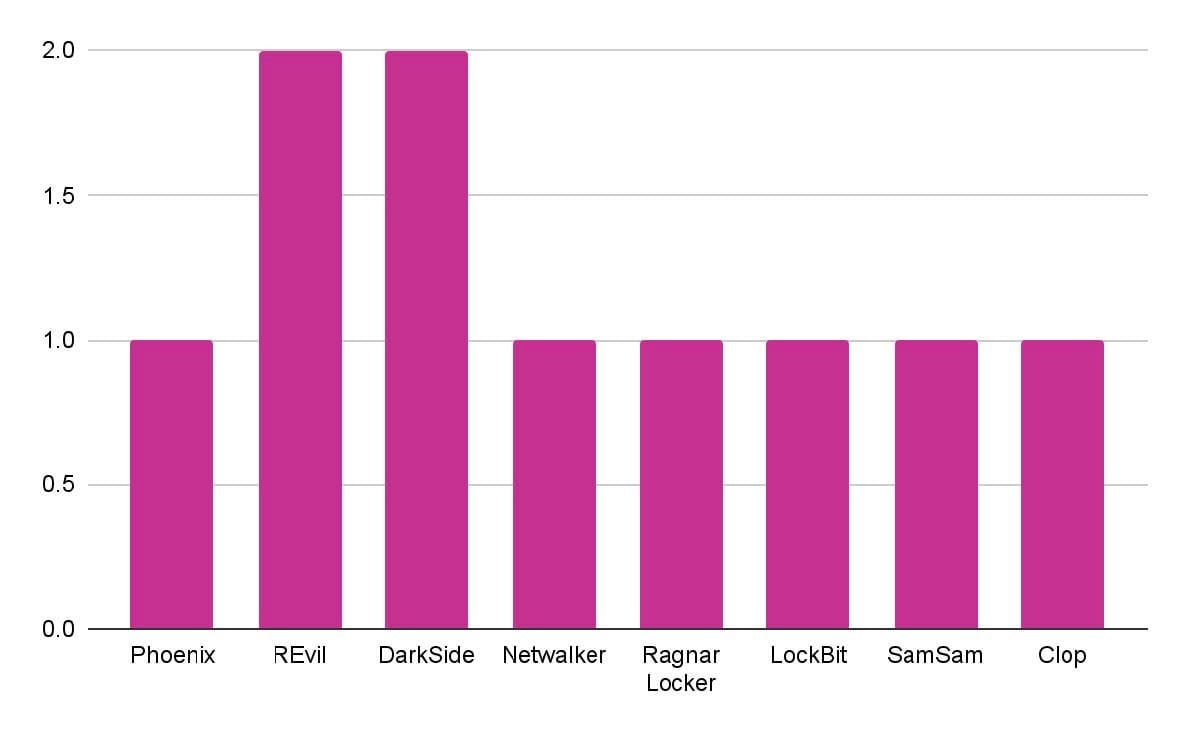
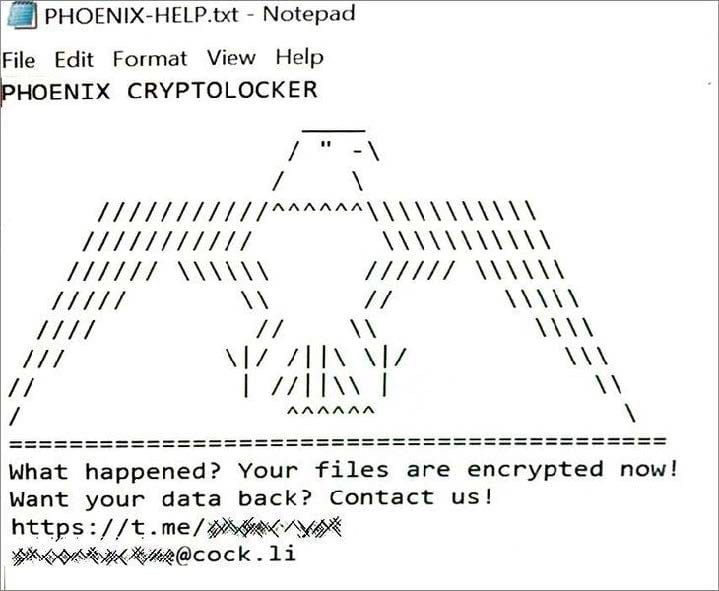
Phoenix CryptoLocker
While Phoenix CryptoLocker has been connected to only one of the top crypto ransomware payments cases, it was responsible for the biggest one at $40,000,000 (CNA Financial), which represents 57.7% of the top crypto ransomware payments. Phoenix is believed to be a newer variant of the ransomware family released by Evil Corp, a Russian-based cybercriminal group.
Evil Corp has allegedly been behind some of the worst hacks of the past decade. Phoenix CryptoLocker entered the list of suspected ransomware variants created by Evil Corp, including DoppelPaymer, Grief, WastedLocker, Hades, and Macaw.
REvil/Sodinokibi
The group REvil/Sodinokibi, and its malware by the same name, were connected to two attacks: JBS USA Holdings Inc. and Travelex, profiting a total of $13,300,000, which represents 19.2% of the top crypto ransomware payments.
REvil/Sodinokibi ransomware is a Ransomware-as-a-Service (RaaS) operation believed to originate from Russia or Eastern Europe, as reports show the group doesn't target Russian-based organizations. Additionally, the ransomware code verifies that the victims are not located in countries belonging to the Commonwealth of Independent States, a regional intergovernmental organization in Eurasia. REvil/Sodinokibi is likely an offshoot of GandCrab, a now-defunct notorious cybercrime gang, as REvil first became active directly after GandCrab shut down, and the malware share a significant amount of code.
DarkSide
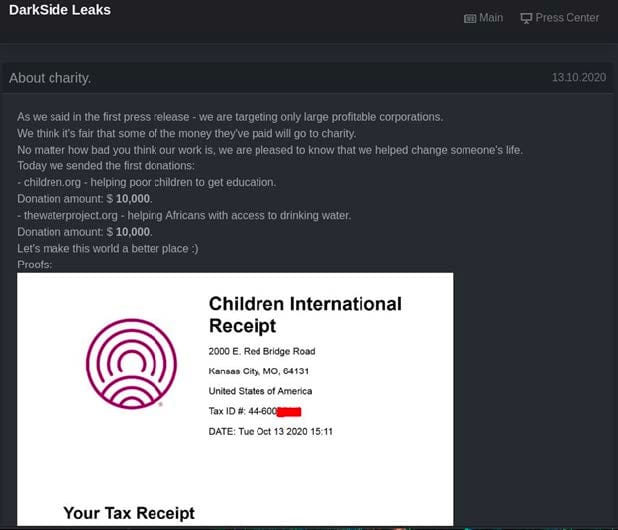
DarkSide was connected to two cases. The group was responsible for the attacks on Brenntag and Colonial Pipeline, profiting a total of $8,800,000, which represents 12.7% of the top crypto ransomware payments.
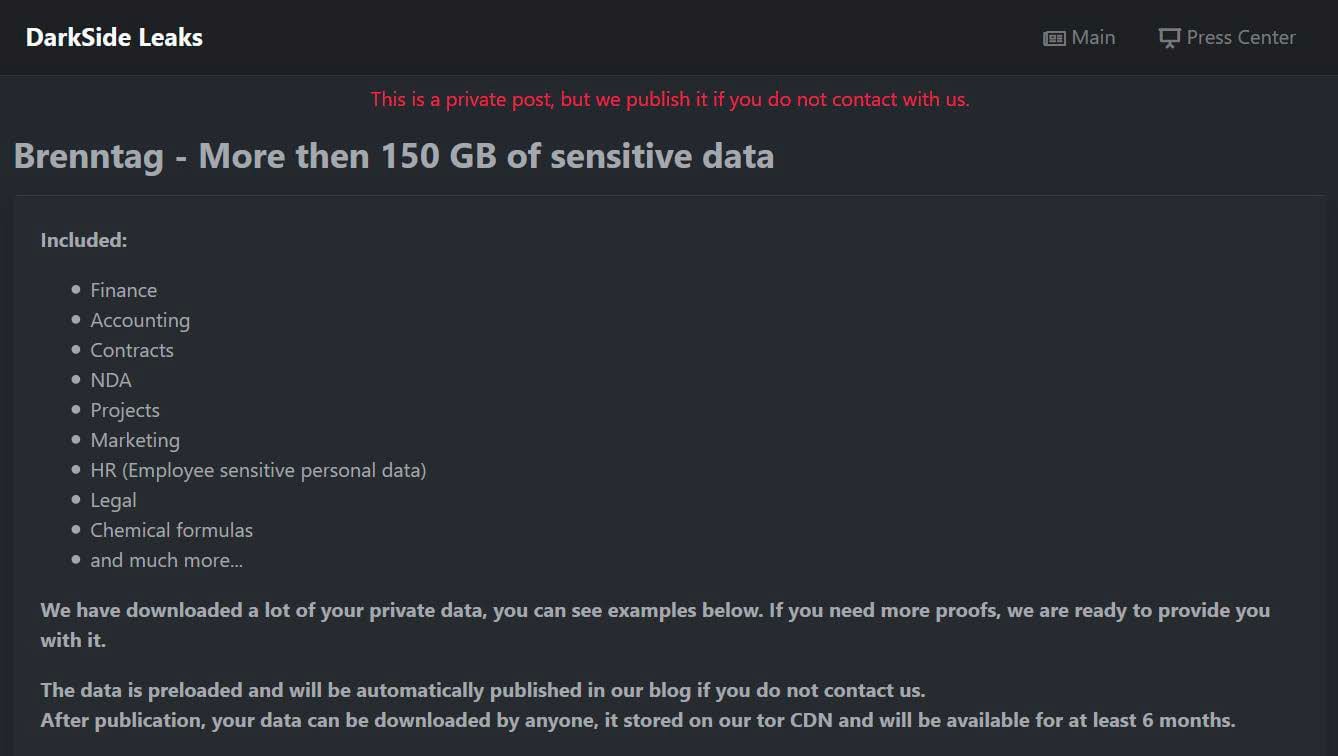
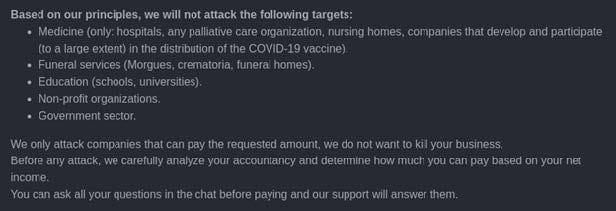
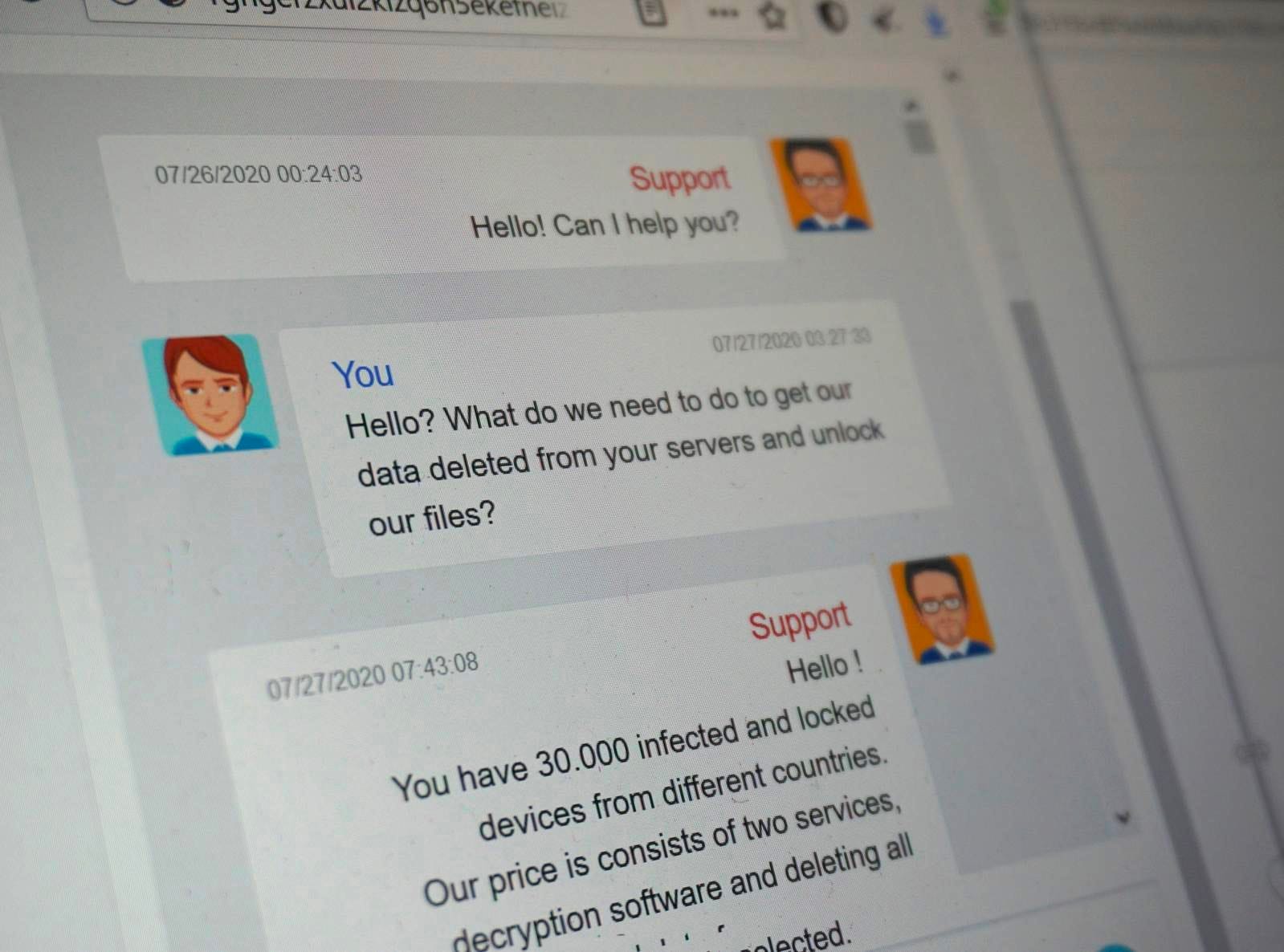
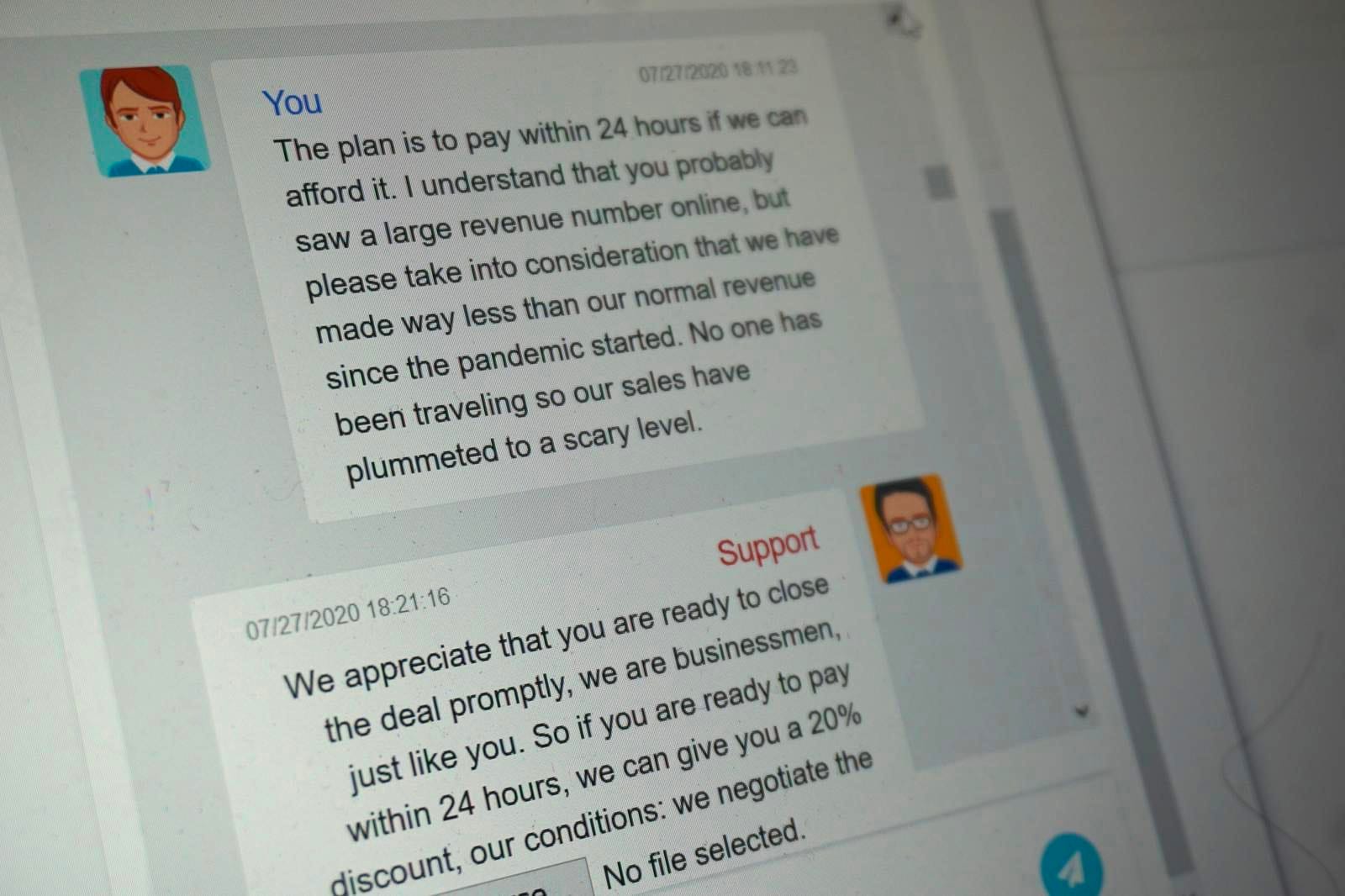
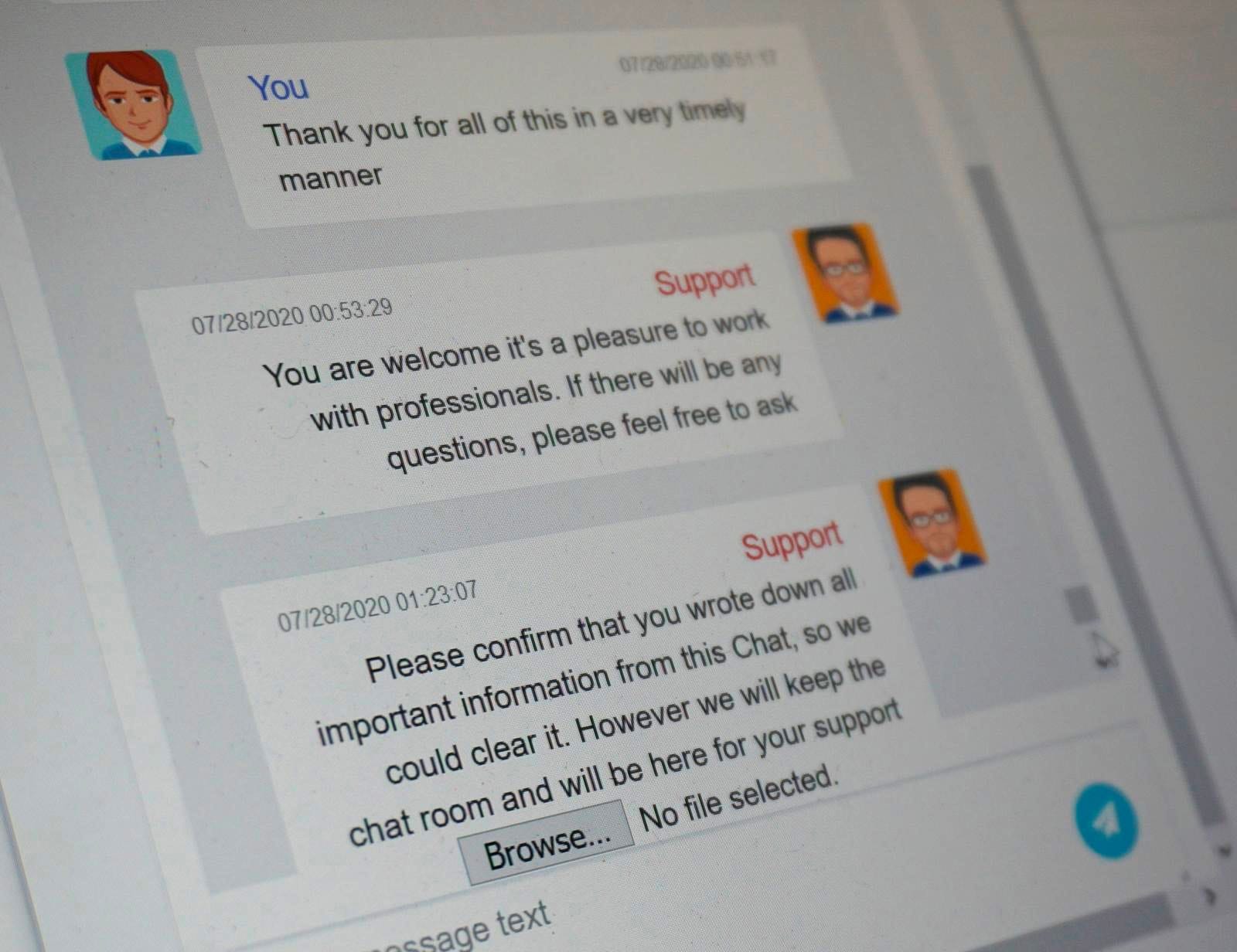
DarkSide is a cybercrime group believed to be based in Eastern Europe that often operates via a Ransomware-as-a-Service (RaaS) model and also employs direct extortion. The group has a history of attempting double ransom payments–in other words, a payment to unlock the affected systems and an additional payment to prevent exfiltrated data from being made public. DarkSide is also known for publishing a code of conduct that lists acceptable targets. These targets are for-profit companies in English-speaking countries. The list of unacceptable targets includes hospitals, hospices, schools, universities, nonprofit organizations, and government agencies. Other protected entities included the Commonwealth of Independent States, a regional intergovernmental organization in Eurasia.
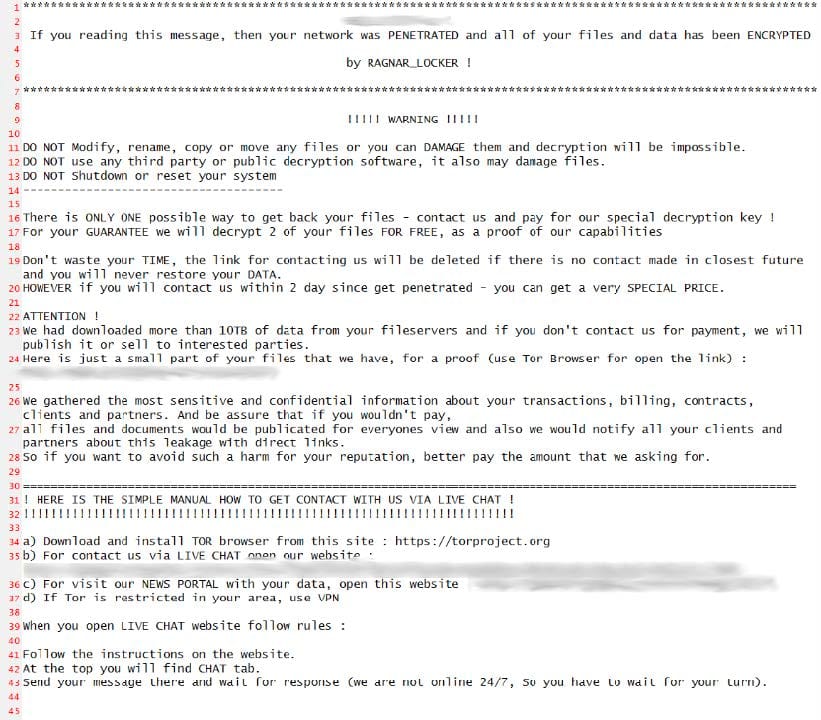
Ragnar Locker
Ragnar Locker was responsible for the CWT attack, the third largest attack on the list, profiting $4,500,000, which represents 6.5% respectively.
Ragnar Locker is the name of the ransomware group and the malware it uses. Similar to DarkSide, Ragnar Locker has been known for the double ransom payment tactic and specifically for regularly changing their obfuscation techniques. The group has often targeted critical infrastructure, such as energy, manufacturing, financial, government, and IT organizations.
Netwalker Ransomware
Netwalker ransomware, designed by the Circus Spider group, was responsible for the UCSF attack, profiting a total of $1,140,895, which represents 1.6% of the top crypto ransomware payments.
The Circus Spider group quickly shifted Netwalker's model to Ransomware-as-a-Service, much like its competitors, to increase its expansion and adoption, allowing them to operate on a larger scale, target more organizations, and increase the size of ransoms. While Netwalker operated like most other ransomware variants, it went further than holding its victim's data hostage. Circus Spider has also been known for immediately leaking parts of the stolen data online at the same time that it demanded the ransom payment. Failure to comply in time meant that Circus Spider would upload the remaining stolen data to the dark web.
LockBit
The LockBit group, one of the largest international ransomware groups, was responsible for the BRB Bank attack, profiting a total of $957,245, which represents 1.4% respectively.
The group is believed to operate out of Eastern Europe and has developed a sophisticated piece of malware called LockBit, named after itself. The group uses the Ransomware-as-a-Service model and frequently invents new ways to beat its competition.
The ransomware is advertised among its community as the fastest and most efficient encryption software and is notable for additional tactics, such as the StealBit malware, which automates data exfiltration. LockBit is used for highly-targeted attacks on corporate and enterprise organizations.
SamSam
The SamSam group, responsible for the Jackson County attack, profited a total of $400,000, which represents 0.6% respectively.
SamSam, also known as Samas or SamsamCrypt, is believed to be created, distributed, and operated from Iran. SamSam has specialized in targeted ransomware attacks, breaking into networks, and encrypting multiple computers across an organization before issuing a high-value ransom demand. A trait of the SamSam group has been to thoroughly monitor networks and user activities for an extended period before demanding a ransom payment.
The group has targeted multiple entities across different industries and critical infrastructure to increase its chance of a big payout for data recovery, such as the transportation, education, and health sectors. While most of the attacks targeted organizations in the United States, other attacks have been reported in the UK, France, Portugal, Australia, Canada, Israel, and the Middle East.
Clop Ransomware
The Clop ransomware, distributed by the TA505 group, was responsible for the University of Maastricht attack, profiting $218,000, which represents 0.3% respectively.
The Clop ransomware, named after the Russian word "klop," which means "bed bug", is believed to be distributed by the Russian cybercrime group TA505. The group is known for its attacks against financial and public institutions and retail companies using malicious spam campaigns and different kinds of malware. The Clop ransomware encrypts pictures, videos, music, databases, and papers, preventing victims from accessing personal data. Urgent data recovery is often necessary for public institutions, which makes them an appealing target for such attacks.
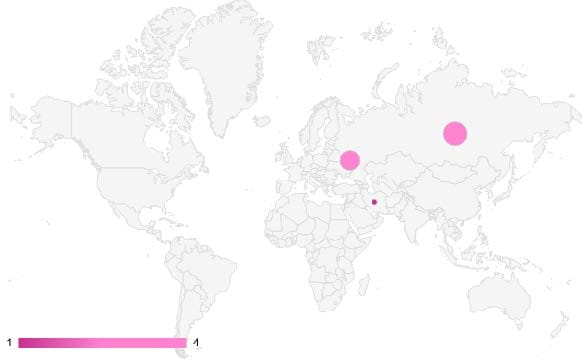
Origin of Detected Ransomware Strains
Bitcoin as a Ransom Payment — Why?
All $69,316,140 in ransom payments was paid in Bitcoin. With several ransom payments in the dozens of millions, it would be challenging to wire such amounts through the legacy banking system without getting caught.
Additionally, it can be difficult even to wire the money in the first place because most of the top ransomware groups operate in high-risk jurisdictions that have tenuous ties with financial systems in Europe and North America.
Lazarus Group, a prolific, North Korea-backed hacking group, has been using Chinese or Malaysian bank accounts to sidestep sanctions. Still, that maneuver would likely only work for smaller amounts rather than upwards of $40 million.
However, with Bitcoin, the amount of money these groups can receive immediately is vastly larger than ransom payments of $100,000 or less because of the decentralized nature of the network. It is unsurprising, then, that ransomware groups have turned to cryptocurrencies.
Despite the wide variety of cryptocurrency options available, such as USDC, Ethereum, or even Monero, ransomware groups have relied on Bitcoin for receiving ransom payments. This choice is likely because Bitcoin is the most well-known and easily accessible cryptocurrency for targeted users and organizations.
Tracing Payments — Is Cryptocurrency Anonymous and Untraceable?
There is now a fast-growing industry of companies that specialize in finding criminals using on-chain data and other techniques, such as Chainalysis, TRM Labs, and Elliptic. Finding criminals is possible because on the Bitcoin network, it's possible to view all addresses that the ransomware recipient address has ever interacted with and potentially trace that chain to the real owner. Everyone leaves a digital trace online.
Clustering is an important technique that aids in unmasking criminals. It works by analyzing Bitcoin blockchain data to find links between addresses and merge them into a group likely to be controlled by the same person or entity.
After the whole blockchain is analyzed, connections appear between the cluster of illicit actors and clusters of services, exchanges, other illicit actors, and personal wallets. This information can then be used to assist in further investigative activities.
Cashing Out — How?
Ransomware groups sometimes use centralized exchanges to convert cryptocurrency into fiat funds. To avoid being caught, they create accounts with fake government IDs purchased on the dark web, but there are pitfalls with that approach discussed below. These groups might also use the crypto directly to buy goods and services like watches, cars, servers, etc.
However, most professional ransomware groups are located in hard-to-reach jurisdictions like Iran, Russia, and North Korea, so they have unique methods of cashing out. For example, ransomware gangs from North Korea are linked to the government and rely on those connections to cash out money through Chinese exchanges. In Russia, it is also possible to cash out dirty money by using the OFAC-sanctioned exchange, Garantex.io, or a lot of other "private" exchanges, which do not care about the source of funds.
Using Exchanges — A Breakthrough for Tracing Back Criminals?
Cybercriminals swap stolen crypto from one blockchain to another, but they are often not cautious enough and use addresses that can lead to their real identities. But most successful investigative cases rely on obtaining information from centralized exchanges. Even when cybercriminals use fake identities on exchanges, they still leave behind clues, such as IP addresses, bank accounts, etc.
As a practical example of how ransomware groups operate, in October 2021, DarkSide moved its Bitcoin funds from one of its wallets in what appeared to be the beginning of a money laundering operation. The group split $6.8 million into seven separate Bitcoin wallets. This tactic made it more difficult to trace the group as it tried to convert the cryptocurrency into fiat. Small amounts were then transferred to exchanges.
Avoiding Detection — What Are the Standard Techniques?
To fight back against traceability, ransomware groups have used obfuscation techniques to increase anonymity and avoid detection.
- Ransomware groups frequently use mixers or tumblers to obscure the destination of their illicit Bitcoin ransom gains.
- Ransomware code is sometimes written in the style of another group to throw investigators off the trail.
- Additionally, the operational security of these groups is very complex. They use operating systems built for security, such as Linux Tails, and have several layers of network connections to obscure their origin, such as VPN->VPN->Dedicated server->TOR network->Dedicated server.
- Most importantly, they use their place of operations as a security layer: Iran, Russia, and the DPRK are all jurisdictions that do not cooperate with foreign subpoenas.
Organization Protection — What Measures to Implement?
Big companies and organizations will always be targets because of their size. However, there are several measures they can take to ensure being targeted doesn't turn into a disastrous ransomware attack.
- First, all organizations should have extensive and regular backups of crucial information, as well as a recovery plan for restoring the data after an attack.
- Second, companies should keep systems and applications up to date to avoid exploitation.
- Third, companies should provide training on common phishing attack vectors and why it's important not to open suspicious email attachments.
- Fourth, companies should use an intrusion detection system and antivirus software.
CDProjekt Red, a videogame development firm based in Poland, is an example of a company that successfully used backups to avoid paying a ransom. In February 2021, the HelloKitty gang hacked the firm. While the group successfully stole the source code of game projects in development and encrypted devices, CDProjekt did not pay the ransom because it had backups to restore the lost data.
Download the full report here.
The full data sources are available below.
1. CNA Financial
2. JBS
3. CWT
4. Brenntag
5. Colonial Pipeline
6. Travelex
7. UCSF
8. BRB Bank
9. Jackson County, Georgia
10.University of Maastricht
For questions about this study or Immunefi itself, reach out at press@immunefi.com
About Immunefi
Immunefi is the leading security platform for crypto, protecting more than $180 billion in user funds, and securing protocols across the full development lifecycle, from pre-deployment through production.